The video industry has seen steady growth in recent years, fueled by the explosion of video content and the ubiquity of the Internet. Protecting this content and securing its delivery are more important than ever.
Digital Rights Management (DRM) is universally accepted as the way to secure video content, services, and more. It also safeguards the broader business offering, private data, and relationships with business partners.
In this blog post, we will discuss the importance of Digital Rights Management for video providers. We will cover various aspects such as preserving service revenue, reducing loss, optimizing video distribution, and more.
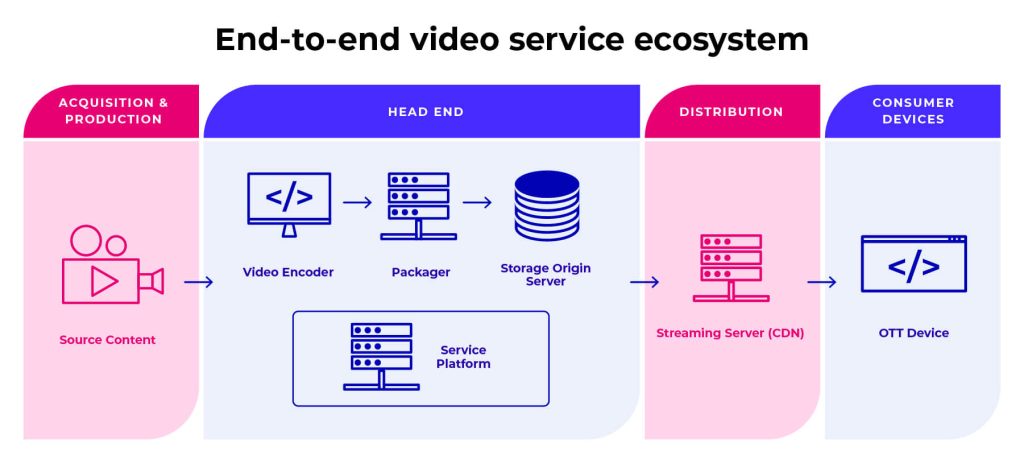
An end-to-end view of the media delivery ecosystem
To protect against piracy, it is essential to have an end-to-end view of the media delivery ecosystem. Understanding this first is key to knowing how to protect it effectively.
The content ingestion process is the core of the ecosystem. This involves a range of interdependent media processing, storage, and software that must work seamlessly together.
Once content is ingested into the service platform and processed, it needs to be delivered to end-users. However, this is not as simple as just sending the content over the internet.
The delivery itself needs to be secured, and the end user must be recognized and authenticated. This is where content entitlements, distribution constraints, and operations roles come into play. These rules ensure content is delivered correctly. It should be sent to the correct user at the appropriate time in the right format and quality.
In addition, consumer devices are prime targets for piracy. This poses further challenges, as there are many categories of devices, each with their own operating systems, chipset environments, video profile, and video packaging requirements. Video providers must maintain multiple protection frameworks to ensure that content is secure across all devices.
Furthermore, the media delivery ecosystem is constantly evolving, with new technologies and devices being introduced regularly. This means that security measures need to be updated and adapted to keep pace with the changes in the ecosystem.
A comprehensive strategy to protect media content must cover every aspect of media delivery, from content ingestion to endpoint delivery. With Digital Rights Management software, video providers can preserve their reputation. It also builds consumer confidence in their services.
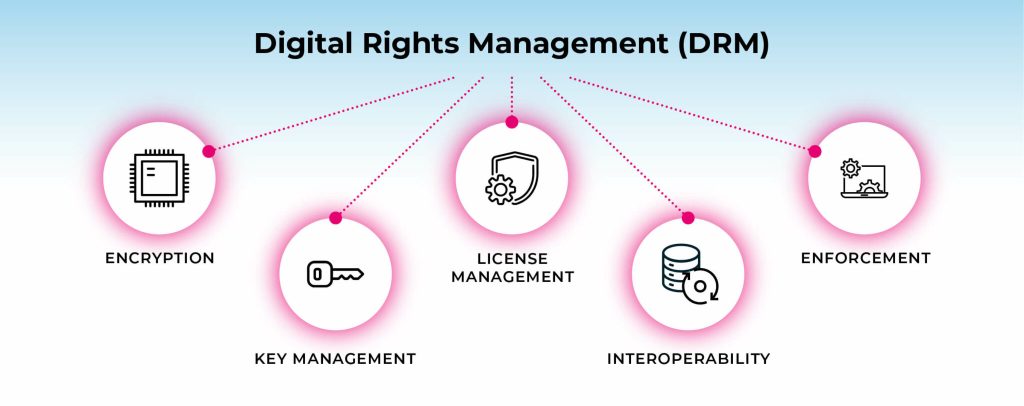
How does DRM work?
- Encryption: DRM software uses encryption algorithms to scramble digital content, making it unreadable without the proper decryption key.
- Key management: The decryption key is typically stored on a server controlled by the content owner or distributor. Users who purchase or license the content are granted access to the key, allowing them to decrypt and access the content.
- License management: The DRM system also uses licenses to control how users can access and use the content. The license defines the terms of use, such as how many devices the content can be played on, how long it can be accessed, and whether it can be copied or shared.
- Enforcement: Enforcement of license terms is managed by DRM software. This software controls access to the necessary decryption key and limits the number of devices that can access the content. DRM may also include anti-piracy measures, such as watermarking or digital fingerprinting, to help identify and track illegal copies of the content.
- Interoperability: DRM systems may also include interoperability standards to ensure that content can be accessed across different devices and platforms.
What are the primary advantages of DRM?
Security should be properly implemented with internal safeguards, procedures, and documentation. This will help video providers reduce their operational costs.
Preserving service revenue
Prioritizing security by upholding consumer access parameters is crucial to guaranteeing the continuation of service revenue. To accomplish this, access permissions must only be granted to end users who have been verified as legitimate and authentic. This can be done using a variety of techniques, including two-factor authentication and password authentication.
Enforcing the total or concurrent user count within a household is another important consideration. By doing so, you may avoid password sharing and guarantee that only permitted users are using the service. Enforcing geographical restrictions can also stop unwanted access from areas where your service is not authorized to operate.
To better understand and model permissible use parameters, video providers can establish baseline criteria for typical households, such as
- Maximum number of devices
- Concurrent users on an account
- Permissible level of license requests
- Consumer’s location
Comparing this baseline with actual use can help identify anomalous use patterns that may indicate piracy. Once anomalous use patterns are identified, mitigation tactics can be implemented via two options: carrot or stick.
A friendly marketing offer can be given to encourage users to comply with the established usage parameters. Alternatively, adjustments can be made to the service to better align with the established parameters or seek legal action against pirates.
These steps allow video providers to protect their service revenue with a proactive strategy that blocks unauthorized access and monitors anomalous usage patterns.
Meeting obligations
To deliver content to end-users, it’s essential that video providers comply with content security requirements and Content Protection Schedules. Content security safeguards the interests of content creators and distributors by ensuring that their content remains secure and accessible to only authorized users.
In addition to consumer-facing safeguards, it’s equally important to protect business terms, such as those between content providers and their distributors. Meeting your obligations is crucial to maintaining positive relationships with your content distributors.
Content Protection Schedules are designed to ensure that video providers meet content security obligations. One such example is Movielabs’ Enhanced Content Protection and Digital Distribution specifications, which help video providers implement a robust security system that protects content from piracy and unauthorized access.
In addition to these schedules, the movie industry has also introduced new production security guidelines. These guidelines secure the interchange of assets between content producers and their partners throughout the entire production process.
Here are some key tips you can take to meet your obligations:
- Understand your contractual obligations: Your distribution agreements will outline the specific requirements and obligations you must meet as a content provider. These may include adhering to content security requirements, meeting production security guidelines, and providing regular reports on content usage.
- Stay up-to-date with industry standards: The video industry is constantly evolving, and new security standards and guidelines are regularly released. To stay compliant, it’s important to stay up-to-date with these standards and implement any necessary changes to your security measures.
- Regularly monitor and enforce compliance: Track usage patterns, conduct security audits, and take action against any unauthorized use or breaches of your security measures.
If obligations are not met, potential breaches of distribution agreements could happen, which can result in no service at all.
Reducing loss
Video content providers face significant challenges when it comes to protecting their content from theft and unauthorized distribution. Content theft can happen in various ways, and it is crucial to reduce losses by implementing effective anti-piracy measures.
One critical step in reducing losses is protecting exclusive sports rights from theft and re-distribution to unlicensed territories. Failure to prevent such incidents by the video provider can result in the licensor refusing to grant or renew rights to distribute their programming. Therefore, video providers must demonstrate that they are executing plans to prevent theft and unauthorized distribution of their content.
In some cases, video distributors have refused to carry original programming due to piracy concerns, as the programmers cannot guarantee against piracy. Paying the price for exclusivity in such cases would not be justifiable. An example of this occurred in 2020, when beIN Media declined to renew its contract with Deutsche Bundesliga over piracy concerns.
To reduce losses and protect exclusive rights, one of the most effective ways is to monitor digital piracy and detect unauthorized access to their content. Providers must identify the sources of piracy and use the information to mitigate the risks of unauthorized access. They can use various digital monitoring tools to detect and prevent piracy, such as web crawlers, watermarking, and fingerprinting.
By prioritizing loss prevention, video providers can preserve their revenue potential while protecting their content. It also ensures that they meet their obligations to content providers and distributors and maintain a good reputation in the industry.
Mitigating risks to advertising revenue
To incentivize users to subscribe to their services, video distributors often provide premium programming at reduced prices or even for free, with the cost offset by advertising revenue. However, there are certain security risks that may harm the reputation of a video provider, such as the existence of fraudulent apps and advertisements.
Some individuals who work for illegal operations could recreate the appearance of a legitimate app through reverse engineering or copying. With this fake app, malicious actors can offer stolen content and services, embed harmful software, or display deceptive ads that lead the user to further danger.
One way to prevent fraudulent apps is to implement measures such as DRM encryption, which can prevent pirates from stealing and redistributing content. In addition, video providers should be vigilant and monitor for any unauthorized use of their content or brand. If fraudulent apps are discovered, they should be reported to the relevant authorities and removed from distribution channels as soon as possible.
Another challenge in the fight against piracy is fraudulent advertising, which can lead users to other threats or scams. To combat this, video distributors can use technologies such as ad verification, which ensures that ads are legitimate and are delivered to the right audience. Advertisers can also use anti-fraud tools such as ad fraud detection and prevention software to identify and block fraudulent ads.
In addition, video distributors can take steps to prevent users from manipulating or skipping ads. This can be done by hardening the viewing application against malicious attacks and monitoring for any unusual behavior.
By taking these measures, video providers can help ensure that their content is protected and that their business is not compromised by fraudulent activity.
Optimizing video distribution
Optimizing distribution is a crucial aspect of video content delivery that requires careful consideration to ensure efficient delivery of content to end-users. However, this process is fraught with risks, such as illegal access to content and spikes in traffic that can result in revenue loss, degraded service quality, and increased costs.
One strategy to optimize distribution is to reduce the cost of CDN capacity by detecting and mitigating illegal traffic on the video provider’s network. By reducing illegal traffic, the cost of carriage can be significantly reduced, freeing up resources for legitimate traffic. This can be achieved through a variety of methods, such as analyzing traffic patterns and implementing measures to block suspicious requests.
Another strategy to optimize distribution is to control CDN access through tokenization. This means that access to content is granted through unique tokens that are encrypted and transmitted securely across the distribution chain. However, tokenization can also be vulnerable to attacks by pirates attempting to steal assets. To mitigate this risk, measures must be put in place to harden against theft and detect attempts to steal authentication data.
In addition to protecting against illegal access, video providers must also ensure that their infrastructure can handle spikes in traffic without degrading service quality. Over-provisioning the network is an expensive solution that may not always be necessary. Instead, optimizing content delivery requires a deep understanding of traffic patterns and the ability to scale resources on demand.
Finally, video providers must be vigilant in detecting and mitigating attacks on the OTT content distribution ecosystem by clandestine actors with illegal intent. This can be achieved through continuous monitoring of network activity and implementing measures to detect and respond to suspicious activity.
Video distribution requires a multi-faceted approach that balances the need for efficient content delivery with the need to protect against piracy and ensure service quality. By implementing the strategies outlined above, video providers can reduce costs, improve service quality, and safeguard their content against illegal access and piracy.
Preserving reputation
Maintaining a positive reputation is essential for video providers who want to stay competitive in the market. One of the most significant threats to a video provider’s reputation is piracy. Consumers expect legitimate sources to provide quality content, and piracy undermines this expectation.
As a result, it is critical for video providers to take steps to preserve their reputation. One of the essential elements of good security is preventing credential fraud, which can lead to numerous threats.
- Hackers often steal databases of consumer IDs and passwords, which they then sell in clandestine markets for a fraction of the original cost. Pirates can use automation to test these credentials against media accounts, and the ones that work are kept aside.
- After obtaining valid credentials, pirates can use them to conduct phishing attacks, which may lead to malware attacks against the unsuspecting account holder. The video provider may then be blamed for the attack.
- By detecting credential fraud through anomalous use, video providers can prevent such attacks, thus reducing the risk to their reputation.
Boosting consumer confidence in video content and services
Implementing DRM and anti-piracy measures alone is not enough. It is also important to communicate to consumers that their content is protected and that their privacy is respected. Good security practices not only protect video content but also boost consumer confidence.
One of the ways to establish trust with consumers is to ensure that your DRM and anti-piracy measures are up-to-date and that they are being implemented effectively. This includes using DRM encryption to protect content, ensuring that user authentication is secure, and implementing measures to prevent unauthorized copying and distribution of content.
Another important aspect of good security practices is transparency. Consumers should be informed about how their personal information is being collected, stored, and used. This includes information on how DRM and anti-piracy measures work, what data is collected, and how it is being used to improve the user experience.
Consumers are more likely to subscribe to a service or purchase content if they feel that their privacy is being respected and their content is being protected. By establishing this trust, content creators and distributors can create a loyal customer base, leading to increased revenue and a stronger business overall.
A comprehensive guide to understand the DRM ecosystem
To help content creators, distributors, and other industry players navigate the complex world of DRM, Verimatrix is proud to offer our “DRM Ecosystem and Security Best Practices” guide!
If you’re looking to protect your video content from piracy and secure your revenue streams, then our ebook is an essential resource. With expert insights, practical advice, and comprehensive coverage of all aspects of DRM, this guide will help you stay ahead of the game and keep your valuable content safe and secure.
Frequently Asked Questions
1. What is DRM?
Digital Rights Management (DRM) is a critical tool for protecting copyrighted digital content. It involves the use of various technologies and measures to control and limit access to digital content, ensuring that only authorized users can access and use it.
2. What content is protected by DRM?
The type of content that is protected by DRM varies depending on the DRM system being used. However, in general, any digital content that is protected by copyright law can be protected by DRM.
This includes:
- Videos (movies, TV shows, etc.)
- Music
- Ebooks
- Software
In addition to protecting specific types of content, DRM can also be used to protect personal information such as usernames, passwords, and payment information. This helps to prevent identity theft and fraud.
3. What is an example of DRM?
One example of DRM in action is the use of digital watermarks. A digital watermark is a unique identifier that is embedded in the digital content itself, often in a way that is invisible to the naked eye. This watermark can be used to identify the original source of the content, track usage, and prevent unauthorized copying and distribution.
In addition to digital watermarks, DRM can also involve the use of encryption technologies. Encryption involves the use of algorithms to scramble data so that it is unreadable without the appropriate decryption key. This can be used to protect digital content such as videos from being accessed by unauthorized users.
These are just two examples of DRM technology that can be used by content creators and providers to safeguard their valuable intellectual property and maintain control over its distribution and use.
4. Can DRM be bypassed?
Determined individuals can often find ways to bypass DRM protections, but this is illegal and can result in legal consequences.





The Counterspy Effect: Operational Efficiency and the End of Piracy Losses