Learn
Top 15 Threats to Video Content Distribution Services
Table of Contents
In our previous article, we established the importance of Digital Rights Management (DRM) and the complexities of video content distribution. Let us now discuss the top threats to video content distribution that the industry must always be vigilant of to reduce the impact on their bottom line.
Widely recognized security threats
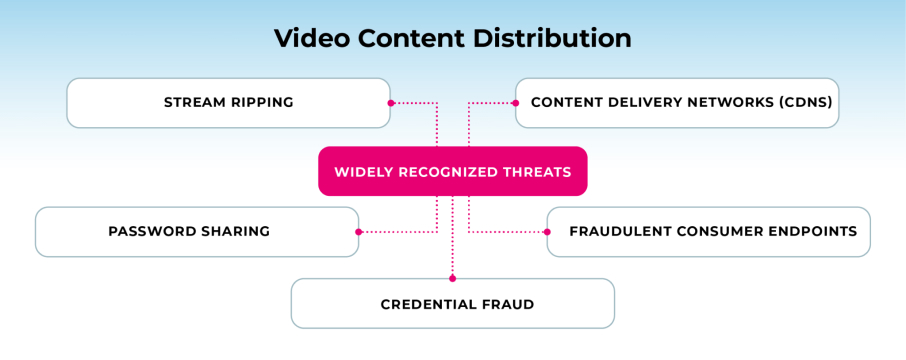
One of the most widely recognized threats in the media and entertainment industry is the theft of content and services for illegal video content distribution online. Some of the main threats include:
- Stream ripping
- Password sharing
- Credential fraud
- Fraudulent consumer endpoints
- Content Delivery Networks (CDNs)
Stream ripping
What is stream ripping?
Stream ripping is a method of illegally obtaining and storing online video or audio content for illegal content distribution. Stream ripping has become a popular method of piracy due to its ease of use and the widespread availability of free and low-cost software tools.
It is also difficult to detect and prevent, as it does not rely on hacking or breaking encryption codes. Instead, it relies on the fact that the video or audio content must be decrypted and played back in order to be viewed or heard, allowing stream rippers to intercept and copy the decrypted stream.
How does stream ripping work?
It involves capturing a streaming video or audio file from a website or application, decrypting it, and saving it as a file on a local computer or server. This method can be accomplished using various tools, such as browser extensions or standalone software programs, which can intercept the stream and save it in a format that can be played back later.
How to prevent stream ripping
In recent years, there have been several high-profile cases of stream ripping, and content providers have been taking measures to combat this form of piracy. One such measure is the use of DRM technologies, which can encrypt the content and restrict access to authorized users.
However, stream rippers have also evolved to bypass these DRM technologies, making it a constant challenge for content providers to protect their content from piracy.
Password sharing
What is password sharing?
Password sharing is a common form of video piracy that involves sharing login credentials for video streaming services with friends, family, or even strangers. This practice allows unauthorized users to access premium content without paying for it, and it has become a major issue for content providers and streaming services.
What is the risk of password sharing?
One of the reasons password sharing is so prevalent is that it is relatively easy to do. Most video streaming services allow users to create multiple user profiles under a single account, and some services even allow simultaneous streams on multiple devices. This makes it tempting for users to share their login credentials with others, allowing them to access the same content without paying for their own subscription.
However, password sharing is not just a problem for content providers and streaming services. It can also be a security risk for users who share their passwords.
When users share their login information with others, they may unwittingly be giving access to their personal information, such as credit card details or browsing history. This information can then be used for malicious purposes, such as identity theft or financial fraud.
How to prevent password sharing
Streaming services have been taking steps to address password sharing, including restricting the number of concurrent streams or introducing additional authentication steps like two-factor authentication.
Despite these measures, password sharing remains a persistent challenge for content providers and streaming services. Content providers and streaming services need to remain vigilant and take appropriate measures to prevent and deter password sharing, while users should be cautious about sharing their login information with others.
Credential fraud
How does credential fraud relate to video content piracy?
Credential fraud is a form of video piracy that involves obtaining and using stolen login credentials to gain access to premium video content without paying for it. Credential fraud can take various forms, but one common method is known as “credential stuffing.”
Credential stuffing involves criminal actors, known as pirates, purchasing large databases of stolen login credentials from the dark web and using automated tools to test the stolen credentials against multiple video streaming services until they find a match.
What is the risk of credential fraud?
Credential fraud is a significant problem for video streaming services and content providers, as it can lead to lost revenue and a damaged reputation. Pirates can use the stolen login credentials to access premium content and distribute it illegally, or they may sell the stolen accounts to others for profit.
How to prevent credential fraud
To combat credential fraud, video streaming services and content providers need to implement tougher security measures to protect their users’ accounts and prevent unauthorized access to premium content.
Two-factor authentication, for example, requires users to enter a second form of authentication, such as a code sent to their phone or email, in addition to their login credentials. IP blocking and behavioral analytics can help detect suspicious login attempts and block access to the service.
Fraudulent consumer endpoints
What are “fraudulent consumer endpoints”?
Fraudulent consumer endpoints refer to any unauthorized means of accessing or distributing digital content, such as video or audio files. This includes media center software and illicit streaming devices (ISDs).
- Media center software is a type of application that enables users to organize, manage, and playback media content, including video, audio, and images, on their computers or home networks. Popular media center software includes Kodi, Plex, and Emby.
- Illicit streaming devices (ISDs) are hardware devices, often sold online or at retail stores, that are specifically designed to access illegal instances of live and series television programming and video-on-demand. These devices are also sometimes referred to as “black boxes” or “fully loaded” streaming devices.
How can fraudulent consumer endpoints be exploited for video content piracy?
While media center software can be a convenient way for users to access and manage their media collections, it can also be used for video piracy. Pirates can create and distribute custom-built media center software, often referred to as pirate apps or add-ons, that allows users to access illegal instances of video content and services.
ISDs are usually small and compact, resembling a USB stick or a small set-top box, and are pre-loaded with pirate apps or add-ons that provide users with access to illegal video content. Some of these devices may even be marketed as legal alternatives to traditional cable or satellite TV services, with claims of providing access to thousands of channels and movies at a fraction of the cost.
These pirate apps or add-ons are typically not available through official app stores or repositories, but rather through unofficial websites or repositories that may be difficult for authorities to monitor or shut down. Once installed, the pirate apps or add-ons can give users access to a wide range of illegal video content, including live and on-demand TV shows, movies, and sports events.
How is this form of video content piracy being shut down?
The proliferation of media center software and ISDs is a significant problem for the video content distribution industry, as it can lead to lost revenue and a damaged reputation.
To combat this form of piracy, video streaming services and content providers have implemented various security measures, such as DRM technologies and watermarking, to protect their content and track its distribution.
Additionally, they work with law enforcement agencies and industry associations to identify and shut down pirate apps and add-ons and take legal action against the individuals and organizations responsible for their creation and distribution.
Content Delivery Networks (CDNs)
What are CDNs?
Content Delivery Networks (CDNs) have become an integral part of the video content delivery ecosystem. CDNs help video content providers deliver their content quickly and reliably to audiences around the world. However, while CDNs have many benefits, they also pose significant challenges to digital rights management and anti-piracy efforts.
How can CDNs be exploited for video content piracy?
One of the main challenges associated with CDNs is that they are open to criminal actors who can gain unauthorized access to video content via open streaming sessions, improperly implemented APIs, or cyberattacks.
CDNs are especially vulnerable to Man-in-the-Middle (MitM) attacks, where an attacker intercepts and manipulates the communication between the CDN and the client. Attackers can use this tactic to steal sensitive data or inject malicious code into the CDN.
Another challenge is that video content delivered through CDNs can be easily copied and redistributed, making it vulnerable to piracy. Once a pirate has access to the video content, they can use it to create unauthorized copies, distribute it through illegal channels, and profit from it.
How can we stop this form of video content piracy?
Video content providers must implement robust DRM and anti-piracy measures. Effective DRM can ensure that only authorized users can access video content, while anti-piracy measures can detect and respond to unauthorized access attempts.
One of the most effective anti-piracy measures is watermarking, which embeds unique identifiers into video content to make it possible to track and trace unauthorized copies. Video content providers can also implement real-time content protection, which uses automated tools to detect and respond to piracy attempts as they happen.
These are just a few examples of the security threats faced by the video content distribution industry. As technology evolves and new threats emerge, it’s essential for content providers to stay vigilant and take measures to protect their content and services.
Additional paths to piracy
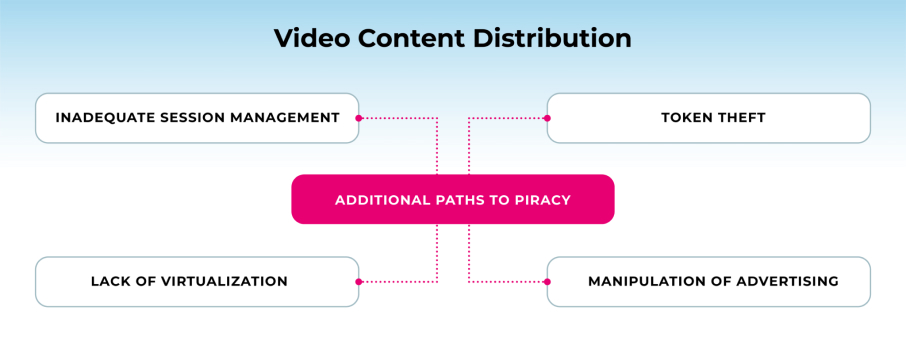
There are several other paths to piracy that video content providers should be aware of:
- Inadequate session management
- Lack of virtualization
- Token theft
- Manipulation of advertising
Inadequate session management
What does inadequate session management mean?
This term refers to the lack of effective control over user sessions, which can allow unauthorized users to gain access to digital media. Inadequate session management can occur due to various factors, such as weak authentication, insecure communications, and improper session management protocols.
For example, a user may log in to a streaming service and then share their login credentials with others, allowing them to access the same content without authorization. Alternatively, a hacker may intercept communication between a user and the streaming service, gaining access to the user’s login credentials and other sensitive information.
What measures are being used to curb inadequate session management?
To prevent inadequate session management, content providers can implement various security measures, such as two-factor authentication, encrypted communication channels, and secure session management protocols. They can also monitor user behavior to detect and prevent unauthorized access to digital media.
Lack of virtualization
How does a lack of virtualization relate to video content piracy?
Virtualization is the process of creating a virtual version of a physical resource, such as a computer system, server, or network. In the context of video content and anti-piracy, virtualization can play a critical role in protecting digital media from unauthorized access and use.
A lack of virtualization refers to the absence of virtualization technologies or policies, which can make it easier for unauthorized users to access and use digital media.
For example, if a video streaming service is hosted on a single physical server without any virtualization, a hacker may be able to gain access to the entire system, including the video content and user data.
How virtualization can prevent video content piracy
Virtualization can help prevent this type of unauthorized access by creating virtual instances of the server or system that can be isolated from each other. This means that even if a hacker gains access to one virtual instance, they will not be able to access other instances or the physical resources that the virtual instances are running on.
Virtualization can also help protect digital media from piracy by allowing content providers to control and monitor user access and usage.
For example, a content provider could create virtual instances of their video streaming service for different user groups, each with its own set of access permissions and usage restrictions. This would allow the content provider to monitor and control user activity, ensuring that the digital media is being used in compliance with licensing agreements.
Token theft
How dangerous is token theft for the video content distribution industry?
Token theft is a type of cyberattack in which an attacker steals authentication tokens that are used to access digital systems or services. Authentication tokens are typically used as a more secure alternative to passwords because they are temporary and can be revoked or invalidated after use.
In the context of video content distribution and anti-piracy, token theft can pose a significant threat to the protection of digital media and the enforcement of licensing agreements. If an attacker is able to steal authentication tokens for a video streaming service, for example, they may be able to access and view digital media without authorization or even distribute it illegally.
How to prevent token theft
Content providers and distributors must implement tougher security measures, such as two-factor authentication and encryption technologies. Encryption technologies can be used to protect authentication tokens during transmission, making it more difficult for attackers to intercept and steal them.
DRM technologies can also be used as an additional measure to prevent token theft and unauthorized access to digital media. Even if authentication tokens are stolen, DRM technologies can be set to limit the number of devices or users that can access a digital media file or to restrict the amount of time that a user has access to the file.
Manipulation of advertising
Why is the manipulation of advertising harmful to the video content distribution industry?
Manipulation of advertising refers to the practice of tampering with digital advertising to achieve unauthorized or deceptive outcomes.
There are several ways in which advertising can be manipulated.
- Ad fraud: Fraudsters create and run fake ads or generate fraudulent clicks on ads to receive payment.
- Ad injection: Unauthorized ads are injected into web pages or mobile apps, often without the knowledge or consent of the user.
- Ad-blocking software: While ad-blocking software may be used for legitimate reasons, such as to improve the user experience or protect privacy, it can also be used to circumvent advertising revenue streams and reduce the profitability of digital media businesses.
How to prevent the manipulation of advertising
Content providers and distributors must implement robust ad verification and anti-fraud technologies. Ad verification involves verifying the quality and legitimacy of ads, as well as ensuring that they are displayed in the correct context and to the intended audience. Anti-fraud technologies can detect and prevent ad fraud, ad injection, and other types of malicious advertising.
Emerging threats
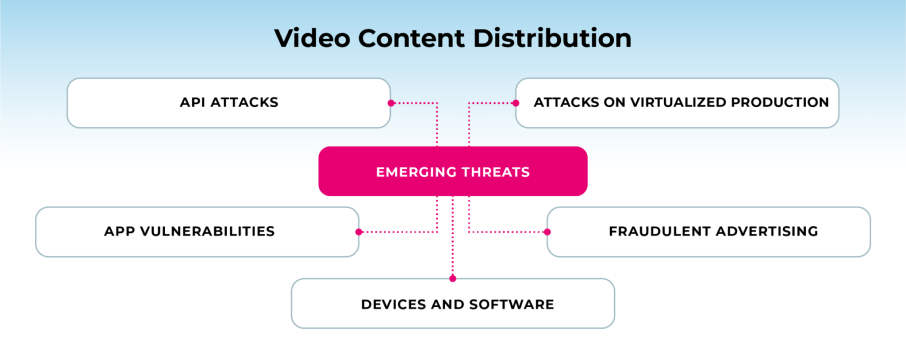
In today’s digital age, video content has become more accessible than ever before, but this convenience has come at a cost: the constant threat of cyberattacks and data breaches.
Video content providers need to be aware of the emerging threats arising from:
- API attacks
- App vulnerabilities
- Devices and software
- Fraudulent advertising
- Attacks on virtualized production
- API attacks
API Attacks
What are APIs?
Application Programming Interfaces (APIs) are points of information exchange between processes, such as consumer requests to interact with a service or between elements in a video content provider’s delivery framework. However, these exchanges also create potential vulnerabilities that can be exploited by attackers.
How dangerous are API attacks for the video content distribution industry?
API attacks can occur in a number of ways. For example, attackers can target video content providers’ payment processing pipelines or other APIs to gain access to sensitive personally identifiable information (PII) data. This information can then be used for fraudulent purposes or sold on the dark web, contributing to the multi-billion-dollar global piracy industry.
How to prevent API attacks
One of the most important measures is to ensure that APIs are properly implemented and secured. This includes using secure communication protocols, such as HTTPS, and implementing access controls to ensure that only authorized users can access the API.
Another key security measure is to implement regular security audits and testing to identify and mitigate vulnerabilities. This can include conducting regular penetration testing and vulnerability scanning to identify potential weaknesses in the API and its surrounding infrastructure.
App vulnerabilities
How dangerous are app vulnerabilities for the video content distribution industry?
For video content providers, app vulnerabilities can pose a significant risk to their business. Attackers can exploit vulnerabilities to weaponize a broadcaster or pay TV operator’s mobile app, stealing consumer PII, content, and services, as well as the video provider’s code or intellectual property.
By reverse engineering the app, attackers can discover vulnerabilities and even create modified versions of the app that contain malicious code or steal sensitive data.
How to protect against app vulnerabilities
Video content providers should implement rigorous security measures. This includes conducting regular security audits and testing to identify and address potential vulnerabilities.
Providers should also consider implementing measures such as code obfuscation, which can make it more difficult for attackers to reverse engineer the app and identify vulnerabilities. Additionally, app developers should follow secure coding practices, such as input validation and secure communication protocols, to reduce the likelihood of introducing vulnerabilities in the first place.
Devices and software
Hardware and software infrastructures of devices used in the production, delivery, and consumption of video content are vulnerable to a range of attacks that can expose sensitive information, such as data, keys, and content.
Cybercriminals can use these vulnerabilities to penetrate the device’s defenses and gain unauthorized access to the video content. Even with compliance requirements in place, devices remain at risk, especially as new technologies emerge and attackers find new ways to exploit them.
For example, attackers can use sophisticated malware and spyware to infect devices undetected and take control of them. Once installed, attackers can collect sensitive information, such as login credentials, and transmit it to remote servers without the user’s knowledge. With access to the device, attackers can gain access to the video content and distribute it without authorization.
Fraudulent advertising
Fraudulent advertising has become a major concern for the video content distribution industry in recent years. In this type of attack, fraudsters use various tactics to gain access to legitimate media apps and exploit them to steal personal information or deliver malicious content to users.
One common method of fraudulent advertising is to create fraudulent apps that look like legitimate ones and then entice users to download them using phishing tactics. Once the user downloads the app, the fraudsters can collect sensitive data or infect the user’s device with malware.
Legitimate advertising delivered to fraudulent endpoints
Another way that fraudsters exploit media apps is by using legitimate advertising services but delivering them to fraudulent endpoints. This means that instead of being displayed to genuine users, ads are shown to bots or other non-human traffic sources. In this way, fraudsters can profit from advertising revenue without actually providing any value to advertisers.
According to a 2021 study by the Digital Citizens Alliance, as much as 40% of advertising through the most dominant online ad platforms is delivered to pirate apps.
Video content providers should work with reputable advertising partners that have anti-fraud measures in place. This includes using sophisticated tools to detect and block fraudulent traffic sources and working closely with advertisers to ensure that their ads are displayed only to genuine users.
Attacks on virtualized production
What is “virtualized production”?
As the media industry continues to move towards cloud-based workflows, virtualized production has become an emerging area of concern for security professionals.
Modern video production relies increasingly on the cloud to enable collaboration among geographically dispersed work groups, exchange assets with outside suppliers of content-related services, and work with business and manufacturing partners.
How can virtualized production be exploited for video content piracy?
In the past, video production was facilities-based, and it was easy to air-gap production platforms so that they had no access to the Internet. However, today’s production practices cannot air-gap the cloud.
As noted in our previous article, the film industry has published distribution guidelines, and initiatives such as MovieLabs’ “Vision 2030” are standardizing cloud-based access, workflow, and security practices. However, as of the outset of 2023, industry stakeholders were still harmonizing their respective platforms with one another and presenting a consistent face to outside resources.
Virtualized production creates new attack vectors for malicious actors. For example, attackers can attempt to gain unauthorized access to cloud-based storage or use malware to steal sensitive data. In addition, the use of third-party services for tasks such as subtitling or audio re-versioning can also introduce new vulnerabilities.
How to safeguard virtualized production
To address these challenges, it is important for the video industry to ensure the safety and integrity of their valuable content throughout the production process.
Strong security measures include employing encryption and access controls, regularly monitoring for suspicious activity, and keeping software and systems up to date with the latest patches and updates. It is also crucial to conduct regular security audits and risk assessments to identify and address any potential vulnerabilities.
Navigating the complex world of DRM with expert insights and best practices
Verimatrix is offering a guide called “DRM Ecosystem and Security Best Practices” to help individuals involved in the video content distribution industry understand the complicated world of DRM!
The guide is designed to assist in protecting video content from piracy and ensuring a secure revenue stream. It contains expert insights and practical advice, covering all aspects of DRM comprehensively. The guide is an essential resource for those seeking to keep their valuable content safe and stay ahead of the game.
Learn how to safeguard video content with this FREE guide
Subscribe to our newsletter
Get the latest anti-piracy insights delivered straight to your inbox.
Talk to us
Modernize network security, protect content from piracy, and achieve studio compliance with Verimatrix. Get your free consultation by completing the form.
We’re here to help
- Find the right solution for you
- Point you to relevant resources
- Explain our pricing
Trusted and Recognized
By industry analysts, associations, and peers



Trusted and Recognized
By industry analysts, associations, and peers