#1 Mobile app protection
Secure your Android and iOS apps, detect & respond to threats, be regulatory compliant.
- One stop shop for all app shielding needs
- Easy and flexible deployment
- Expert guidance and implementation
Judge us by the companies we keep.







Extended Threat
Defense (XTD)
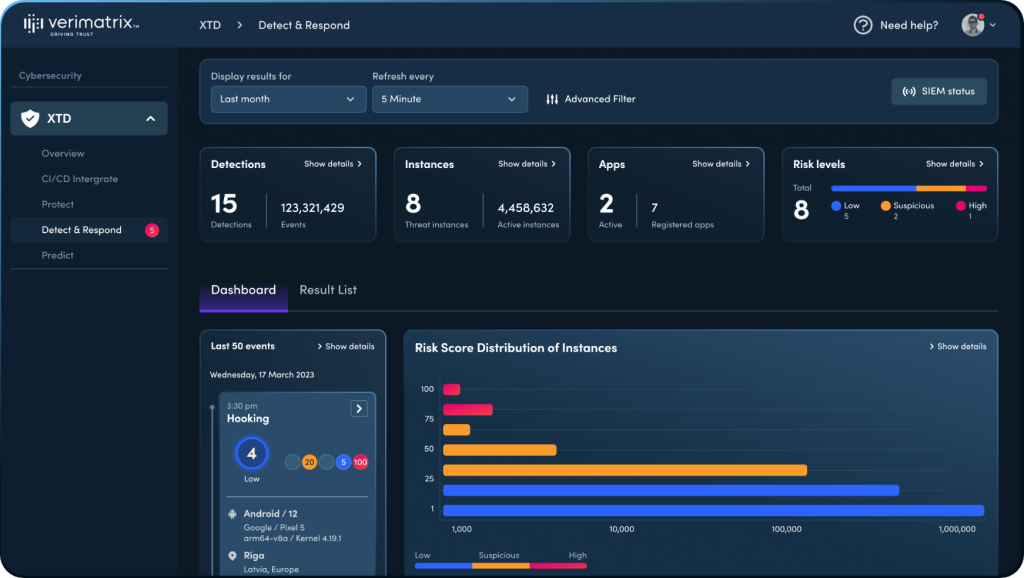

Protect your enterprise
from blind spots.
Verimatrix XTD extends beyond your existing MTD and EDR security to protect threats from unmanaged devices. Powered by AI/ML, detect and respond to threats before your enterprise is compromised.
Tackling the fastest growing
attack surface.
While many organizations have some form of cybersecurity protection for their managed devices (employee devices), XTD is one of the only cybersecurity solutions to address multi-vector threats stemming from unmanaged (consumer) mobile devices.
Managed (Employee)
Security agent installed on employee devices.
Most enterprises use existing comprehensive mobile and endpoint security to protect employee devices.
Cybersecurity, extended
Unmanaged (Consumers)
No security agent installed on customer devices.
Most enterprises only have basic app security to satisfy app store requirements.
As the number of apps grow, so do attack surfaces. Hackers take advantage of security vulnerabilities from connected apps to infiltrate critical IT infrastructure and deploy threats including phishing, ransomware, zero-day attacks and others.
XTD predicts, prevents, detects, and responds to these threats before they can cause damage to an organization.
Techniques we deploy.
Verimatrix XTD provides multi-layered in-app protection combining a range of advanced security techniques.
Get started. Faster.
XTD’s proprietary zero-code technology allows customers to add deep, defensive countermeasures without the hassle of integration.
Inject protection into mobile apps with ease. XTD's advanced protection does not require end users to install a separate security agent.

XTD integrates directly into a CI/CD workflow, enabling developers to seamlessly integrate powerful security without delaying the app development process.
Tailor-made to meet your security needs, XTD’s SIEM-integrated platform allows you to cut through the noise and identify high-risk threats.
OWASP Mobile Top 10
What are the OWASP Top 10 mobile vulnerabilities? What impact do they have? Read our developer guide to get the full picture of threats facing mobile apps and how to deal with them.
Trusted by CISOs and
security experts alike.
Security Operations Center (SOC)
Deploy powerful countermeasures to thwart attacks.
- Detect, investigate, and respond to cybersecurity threats.
- Ensure all connections to IT infrastructure, including unmanaged devices, are fully secure from mobile cybersecurity threats.
- Leverage mobile threat intelligence to prepare and defend against future attacks.

CISO/CIO
Gain full visibility of security risks enterprise-wide.
- Secure mobile applications developed by your organization.
- Futureproof information and data security programs.
- Protect revenue streams.
- Meet all compliance requirements.
- Ensure a seamless customer journey.
Fraud Prevention Department
Prevent sophisticated fraudsters from infiltrating your organization.
- Thwart fraudulent intrusion attempts.
- Protect data layers from being infiltrated and exfiltrated.
- Manage incident workflows, assess risk statuses, and plan action.

R&D, Engineering, Product
Develop secure apps with ease.
- Apply security with zero code and agentless.
- Ensure proper security protection within apps.
- Incorporate XTD as part of a CI/CD integration.
Protecting the apps that
drive the digital economy.
If your enterprise has an app, you need XTD.
Asaf Ashkenazi, CEO of Verimatrix, reveals how hackers are using apps to gain access to an enterprise’s critical IT infrastructure, and how we built XTD to stop them in their tracks.

VMX
labs
Stay in the loop with VMX Labs, our cybersecurity resource hub. Explore the latest threat advisories and commentaries from experts.









3 Security Imperatives for Vehicle App Manufacturers in 2024