Having covered the complex nature of the media delivery ecosystem and the issue of online piracy in other articles, we can now address the DRM technology used to safeguard video content distribution here. Specifically,
- Tokenization
- Geo-filtering
- Forensic watermarking
- Static and dynamic protections
As video delivery has transitioned to streaming service models delivered over the Internet, Digital Rights Management (DRM) has allowed video providers to maintain their reach among audiences that no longer rely on traditional pay TV or physical media for content consumption and to reach new ones.
DRM technology is viewed by operators as providing strong security for content and services. However, security attacks can occur before and after encryption by the DRM platform, as well as on the encrypted content itself. This means that DRM technology alone cannot fully protect delivery, service endpoints, or an operator’s service delivery infrastructure.
The importance of multi-DRM systems in content protection
Multi-DRM systems are designed to enable multiple DRM technologies to work in harmony, providing a comprehensive and robust approach to content protection.
The risks of single DRM systems
While single DRM systems may provide some level of protection, they are not without their limitations and vulnerabilities. There are two major risks:
- Inability to protect against all forms of piracy or hacking: For example, some single DRM systems are more effective at preventing piracy through file sharing, while others are better at protecting against screen capture or stream ripping.
- Obsolescence over time. As technology evolves and new methods of piracy are developed, single DRM technologies may become less effective at protecting digital content. In some cases, a single DRM system may even be cracked or circumvented, rendering it useless for protecting content.
How to choose the right multi-DRM system
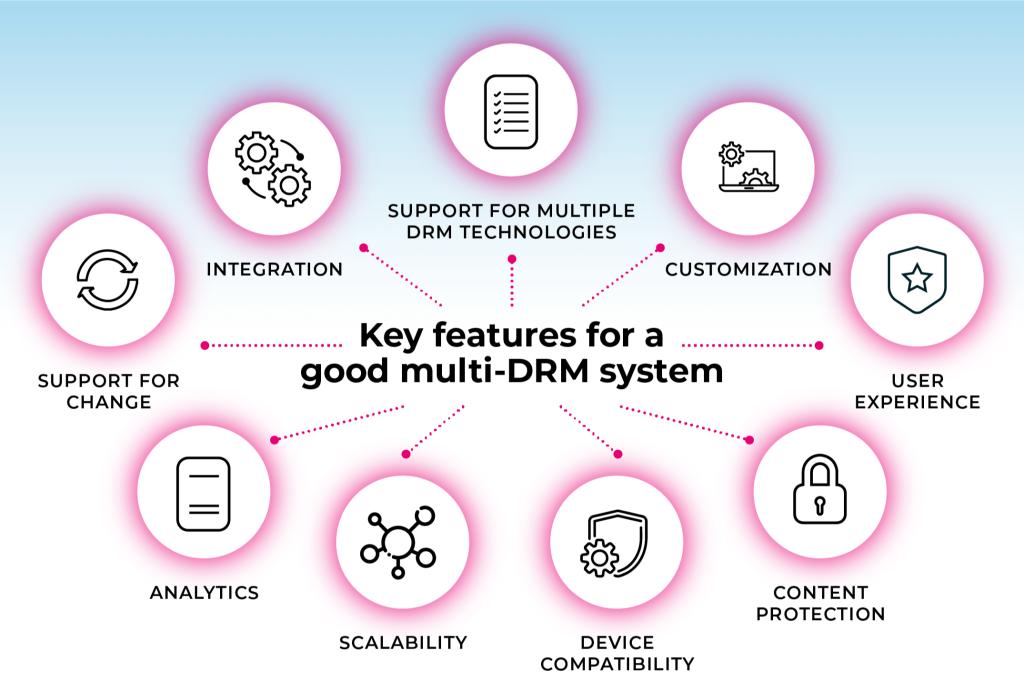
Multi-DRM systems come with a range of features that enable effective and efficient content protection. Here are some of the nine key features to look for when choosing a multi-DRM system:
- User experience: The multi-DRM system should provide a seamless user experience for viewers, allowing them to access and view content on their preferred devices and platforms.
- Content protection: The ability to mitigate and/or prevent a range of threats, including screen capture, stream ripping, and file sharing.
- Device compatibility: Playback support on multiple devices and platforms, including desktops, mobile devices, and smart TVs.
- Scalability: The ability to scale as your content distribution needs grow. This includes support for large volumes of content, multiple distribution platforms, and different licensing options.
- Support for multiple DRM technologies: The most important feature of a multi-DRM system is support for a range of DRM technologies, including the ones that are widely used in your target markets.
- Support for change: Multi-DRM systems are designed to accommodate changes to individual DRM technologies as they evolve and new ones as they emerge.
- Analytics: The system should provide detailed analytics on content usage and consumption, including viewer data and usage patterns. This will enable you to optimize your content delivery and improve user engagement.
- Customization: The system should be customizable to meet your specific content protection needs, including the ability to choose which DRM technologies to use for each platform.
- Integration: The ability to integrate with your existing content management and distribution systems, such as a content delivery network (CDN) or a video player. This will make it easier to manage and deliver your digital content and ensure a smooth user experience for your viewers.
By choosing a multi-DRM system like Verimatrix Streamkeeper Multi-DRM that offers these key features, content owners can ensure that their digital content is protected against a wide range of threats while still allowing for easy access and viewing by legitimate users.
What is tokenization?
In today’s digital age, content piracy has become a significant problem, leading to lost revenue for content creators and distributors. DRM is a crucial technology used to protect digital content by controlling access to it and preventing unauthorized distribution.
One method that has gained traction in recent years is tokenization. Tokenization has become a popular method of securing digital content because it involves creating unique tokens that are used to access digital content, which provides enhanced security and improves the user experience.
Benefits of tokenization in DRM
- Increased security and protection against piracy: Tokens are unique to each user or device and are created using complex algorithms, making them difficult to replicate or counterfeit.
- Enhanced user experience and convenience: When users have access to tokens, they can easily and conveniently access the digital content they want without having to go through a lengthy authentication process.
Drawbacks of tokenization in DRM
- Complexity and cost of implementation: Tokenization can be a complex process, requiring specialized knowledge and technical expertise. Implementing tokenization can also be expensive, particularly for smaller content providers who may not have the resources to invest in the technology. Additionally, tokenization requires ongoing maintenance and updates to ensure that the tokens remain secure and effective over time.
- Potential for tokenization to impede content accessibility: Tokenization can potentially impede content accessibility, particularly for users who may not have access to the necessary technology to generate or use tokens. Additionally, tokenization can restrict access to content based on user location or other factors, which may limit the availability of digital content for certain users.
What is geo-filtering?
Geo-filtering is a content protection technique that restricts access to digital content based on the geographic location of the user. The purpose of geo-filtering is to limit access to digital content based on legal, regulatory, or commercial considerations.
A company may only have the rights to distribute a particular movie or TV show in certain countries or regions, and so they will use geo-filtering to ensure that users outside those areas cannot access the content.
Is geo-filtering legal?
Yes, geo-filtering is legal. It is widely used across various industries, including media, gaming, and e-commerce.
Examples of geo-filtering in action include streaming platforms that restrict access to their content based on the user’s location, online stores that limit the sale of certain products to specific regions, and gaming companies that restrict access to certain games based on the user’s location.
However, geo-filtering can be controversial as it can limit access to legitimate users. For example, a user who is traveling outside their home country may be unable to access content that they have paid for because of geo-filtering. Additionally, geo-filtering can be easily bypassed by using a virtual private network (VPN) or proxy server, which makes it ineffective against determined pirates.
How does geo-filtering work?
Geo-filtering works by identifying the user’s IP address and comparing it to a list of approved or restricted locations. There are several techniques that can be used for geo-filtering.
- DNS-based: Redirecting users to different servers based on their geographic location.
- VPN/proxy detection: Identifying users who are accessing content through a VPN or proxy server and then blocking their access.
- IP-to-location mapping is the most commonly used technique for geo-filtering. It involves mapping the user’s IP address to their geographic location using a database of IP addresses and their associated locations.
Limitations of geo-filtering
- Inaccuracies in IP-to-location mapping: IP addresses can be dynamic and change frequently, which can make it difficult to accurately map them to a specific location.
- Easy to bypass: Geo-filtering can be easily bypassed by using a VPN or proxy server. These services allow users to mask their IP address and appear as if they are located in a different region, which can allow them to access content that would otherwise be restricted.
- Limited to IP-based content: Geo-filtering is limited to content that is delivered over the internet and relies on IP addresses for location data. This means that content that is delivered through other channels, such as physical media or satellite broadcasts, cannot be geo-filtered.
Best practices for geo-filtering
- Understand your audience and their needs. Having a clear understanding of your audience’s geographic distribution will help ensure that legitimate users are not unnecessarily restricted.
- Use multiple geo-filtering techniques for improved accuracy. While IP-to-location mapping is the most commonly used technique for geo-filtering, using multiple techniques can improve the accuracy of the filtering process.
- Monitor and adjust geo-filtering rules. Geo-filtering rules should be monitored regularly to ensure that they are working effectively and accurately.
What is forensic watermarking?
Forensic watermarking is a technique that involves embedding a unique, invisible identifier into digital content, such as videos, to identify the source of unauthorized distribution so that every instance and every individual stream can be associated with an authorized, authenticated user or singled out as potentially being stolen.
Unlike traditional watermarking, which is intended to be visible and can be easily removed, forensic watermarking is designed to be undetectable and to withstand any attempts at removal or alteration.
Forensic watermarking has become increasingly popular in recent years, and many industries are using it to protect their content from piracy. For example, the film and television industries and sports leagues are all using forensic watermarking to protect their copyrighted content.
There are many real-life cases where forensic watermarking has been crucial in identifying piracy. For example, in 2015, a pirate group was arrested in the United States for distributing copyrighted movies and TV shows. The forensic watermark embedded in the content was used as evidence in court, resulting in a successful prosecution.
Advantages of forensic watermarking
- Identifying the source of piracy: When a pirated copy of a video is discovered, the forensic watermark can be extracted and used to identify the source of the leak in the distribution chain. This allows content owners and distributors to take legal action against pirates.
- Versatile: Forensic watermarking can be applied at different stages of the content creation and distribution process. For example, forensic watermarks can be added during post-production or content delivery.
- Reliable: Forensic watermarks are embedded at a low level in the content, making it difficult to remove or alter.
Limitations of forensic watermarking
- False positives: Forensic watermarking can sometimes result in false positives, where legitimate content is flagged as pirated. This can occur if the watermark is damaged or removed during the distribution process, or if it is not properly configured.
- Limited protection against physical piracy: Forensic watermarking is designed to protect digital content from piracy. It cannot protect against physical piracy, such as the creation of counterfeit DVDs or Blu-ray discs.
- Limited effectiveness against live streaming: Forensic watermarking is less effective in identifying piracy from live streaming events, as pirates can use different devices and platforms to stream the content.
Best practices for implementing forensic watermarking
- Select a reliable forensic watermarking provider. Choose a provider that offers reliable forensic watermarking technology and has a proven track record of combating piracy.
- Customize the watermark. Including unique identifiers and metadata in the watermark can help identify the source of piracy more accurately.
- Embed the watermark early in the distribution process. It’s recommended to do so during the encoding or transcoding stage to ensure that it is present throughout the entire distribution chain.
- Regularly test and update the watermark. Ensure that the watermarks are still effective in identifying piracy and are not being circumvented by pirates.
Mastering DRM: Get additional insights into the complex world of DRM technology
Verimatrix has created a guide titled “DRM Ecosystem and Security Best Practices” to provide guidance to those involved in the distribution of video content. The guide aims to help individuals understand DRM better and provide practical tips on how to use DRM technology more effectively, both on its own and in combination with other technologies and best practices.
The guide offers expert insights that cover several aspects of DRM comprehensively. It is an invaluable resource for those looking to protect their valuable content and maintain a secure revenue stream. By utilizing this guide, individuals can stay ahead of the game and ensure the safety of their video content.
Protecting legitimate software and apps from hackers and piracy
It is essential to protect software and applications, both at rest and during operation, to prevent them from being exploited maliciously. If this step is not given serious attention, software and app developers may face a significant risk of the time, money, and resources they put into creating digital content being wasted.
The current state of piracy and hacking in the software and app industries is alarming. Pirates and hackers analyze and reverse-engineer legitimate apps to create fraudulent ones that look like their authentic counterparts. These fraudulent apps are then used to attack consumers and steal their personally identifiable information (PII) or access the video provider’s infrastructure to steal content and services.
To ensure software and apps are well-protected, two types of safeguards are required: static and dynamic protections. Static protections hide the app’s internal structure, software components, and interfaces to obscure any attempted tampering. Dynamic protections, on the other hand, detect any interception attempts of keys and data during runtime.
What are static protections?
Static protections in DRM are a set of techniques used to safeguard apps from reverse engineering and tampering. These techniques are applied at the time of application development and compile time. Once the app is compiled, these protections become part of the app, making it more difficult for hackers to reverse-engineer and tamper with it.
Types of static protection
There are different types of static protections, such as code obfuscation, white-box cryptography, and software tamper resistance. Each technique has its own strengths and weaknesses, and the choice of technique depends on the requirements of the application and the level of protection needed.
- Code obfuscation: Used to obscure the code and make it difficult to understand. This technique modifies the code structure, replaces function and variable names with meaningless names, and removes code comments. By doing so, it makes the code harder to understand and, therefore, harder to reverse-engineer.
- White-box cryptography: Used to encrypt and decrypt data within the application while keeping the encryption and decryption keys secret. This technique ensures that even if an attacker gains access to the application code, they will not be able to extract the keys and decrypt the data.
- Software tamper resistance: Used to protect the application from tampering by detecting and preventing any attempts to modify the application code. This technique involves adding integrity checks to the application code, which verify that the code has not been modified since it was compiled.
Best practices for implementing static protections
- Regularly review and update your static protections to ensure they are up-to-date and effective against the latest threats.
- Test your static protections thoroughly to ensure they are working as intended and not interfering with the normal functioning of your app.
- Use a combination of static protections for layered security.
- Educate your team and users about the importance of security and best practices for protecting sensitive data.
- Follow industry standards and best practices for app security.
What are dynamic protections?
Unlike static protections, dynamic protections are a set of techniques that are implemented during runtime, which means that they are applied as the content is accessed and viewed. This allows for more flexibility in adapting to new threats and attacks.
Dynamic protections are used in a variety of industries beyond video content distribution, including software development, financial services, and online gaming. In these industries, dynamic protections are used to prevent hacking, fraud, and other forms of cyberattacks.
Specifically for the video content distribution industry, dynamic protections are used to detect attempts to intercept keys and data during runtime. This can help prevent unauthorized access to the content, which is critical for protecting the intellectual property of content owners and ensuring that they can monetize their content.
Types of dynamic protection
Each dynamic protection technique has its own advantages and disadvantages, and content owners must carefully consider which techniques to use based on their specific needs and resources.
- Tamper-proofing: Add checks to the DRM system to detect if the code has been modified or tampered with.
- Encryption: Encrypt the keys and data in order to make it more difficult for attackers to intercept them.
- Behavioral analysis: Monitor the behavior of the user and the DRM system in order to detect abnormal behavior that may indicate an attack.
- Real-time monitoring: Monitor the system in real-time in order to detect and respond to attacks as they happen.
Benefits of dynamic protections for content owners
- Enhanced security: By using a combination of techniques, dynamic protections provide a much higher level of security than traditional DRM solutions. This makes it much harder for attackers to access and distribute video content without authorization.
- Better control over content distribution: Content owners can use dynamic protections to enforce licensing agreements and access controls. This ensures that their content is only accessed by authorized users, which helps to protect their revenue and brand reputation.
- Increased revenue: By preventing unauthorized access to video content, dynamic protections help to ensure that content owners receive payment for their content.
- Valuable insights into content consumption: Content owners can use analytics tools to track user engagement and behavior, which can help them make better decisions about content distribution and marketing.
Best practices for implementing dynamic protections
Implementing dynamic protections can be a complex process that requires careful planning and consideration. Here are some considerations for integrating dynamic protections into existing DRM systems:
- Identify your security requirements. Before implementing dynamic protections, it’s important to identify your security requirements and the level of protection needed for your video content. This will help you select the appropriate dynamic protection techniques and ensure that your DRM system is adequately secured.
- Choose the right dynamic protection techniques. There are several dynamic protection techniques available, each with their own advantages and disadvantages. It’s important to carefully evaluate each technique and choose the ones that are best suited for your specific needs.
- Integrate dynamic protections into your existing DRM system. Integrating dynamic protections into an existing DRM system can be challenging, as it may require modifications to the system’s architecture and code.
- Monitor and update your dynamic protections. Dynamic protections are not a one-time solution, and they must be monitored and updated on an ongoing basis in order to stay effective against new and evolving threats.







The Counterspy Effect: Operational Efficiency and the End of Piracy Losses