Security solutions for
Content Protection
Monetize video content distribution from origination to playback.


Overcome obstacles throughout the content workflow.
Secure, scalable and comprehensive solutions are critical to protect content during every stage of the workflow – especially as release windows shrink and attack surfaces expand. To avoid costly churn and gain subscribers, content owners and video service providers need to prioritize robust security without detracting from user experience.
Bulky security creates subpar UX
Protecting content distribution shouldn’t come at the cost of a seamless user experience. Providers need powerful yet elegant security to offer consumers sleek, simple log-in and viewing sessions.
Increasingly strict regulations
Content owners are mandating ever increasing regulations for the protection of content workflows and streaming apps. The right security approach will help you achieve compliance and gain access to premium content.
Sophisticated piracy threats
As piracy evolves, the days of camcording have been replaced with more sophisticated attacks. It is now necessary to detect and prevent piracy at every stage of delivery, before content ever reaches the client device.
A Comprehensive Guide to Digital Rights Management
Introducing the DRM Ecosystem and Security Best Practices Guide – a comprehensive manual on how to protect your online video content from hackers and pirates. Don’t let them win!
Reap the benefits of an all-in-one content security platform.
Powerful security meets a seamless user experience
Protecting premium content and creating sleek playback experiences shouldn’t be at odds. Frictionless log-ins, seamless transition from device to device, and viewing experiences uninterrupted by bandwidth issues are critical to avoid costly subscriber churn. Verimatrix protects your business by safeguarding the entire content workflow with easily implemented solutions that enhance user experience.
Prevent attacks with solutions that go beyond compliance
As content distribution models change, cybercriminals and pirates are developing more sophisticated attacks to gain access to data, content, and valuable intellectual property. The right security approach will do more that meet minimum requirements set by content owners – it will safeguard your business and prevent a wide range of attacks.

Keep pirates out of your content workflow
Pirates steal more than just your content – they rob legitimate video service providers of subscribers by attracting consumers with reduced prices and advert free premium content. The ability to quickly detect the source of piracy and shut down hackers with automated solutions is key to safeguarding your business and retaining subscribers.

Solutions for end-to-end content protection.
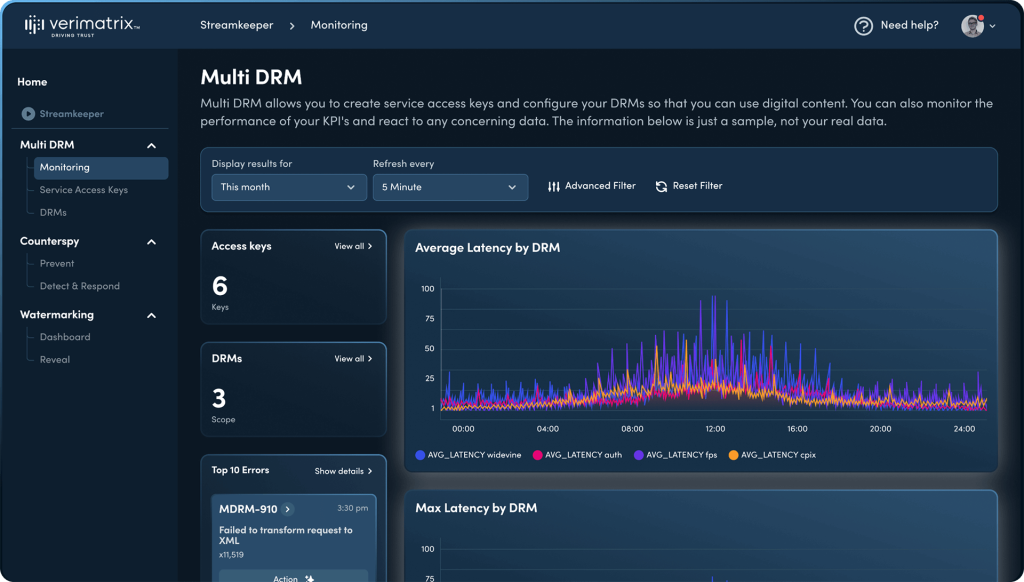
Streamkeeper
Anti-Piracy Solutions
Verimatrix Streamkeeper delivers studio-approved digital content security combined with military-grade app shielding and automated anti-piracy countermeasures to provide operators with a fast, easy, and effective way to hunt down and take out pirates. It’s the complete content security package that’s consistently proactive, not just reactive.

Verimatrix VCAS
Vermatrix VCAS solutions are pre-integrated with a vast global ecosystem and have proven interoperability with subsystem providers (including billing, encoding, middleware and application vendors). This gives you the freedom to work with partners of your choice for your video content workflow needs – all while maintaining studio-compliant security levels.
Awards & Accolades

Verimatrix Streamkeeper wins Gold in Telecom Innovations

2023 NAB Show Product of the Year Award

Verimatrix Streamkeeper™ Named Best Content Protection Technology

Verimatrix Streamkeeper™ Wins the Revenue Security Award 2022
For all things security, Verimatrix has you covered.
For over 29 years, Verimatrix has empowered our customers and partners to secure everything from Hollywood content and live streaming sports, to sensitive financial and healthcare data, to mission-critical mobile apps, connected cars, IoT, gaming and eSports.

Monica Rayo
COO at Agile Content
Talk to us
Modernize network security, protect content from piracy, and achieve studio compliance with Verimatrix. Get your free consultation by completing the form.
We’re here to help
- Find the right solution for you
- Point you to relevant resources
- Explain our pricing
Trusted and Recognized
By industry analysts, associations, and peers



Trusted and Recognized
By industry analysts, associations, and peers