Watermarking
Track the source of piracy within minutes.
Watermarking identifies the source of distribution, ensuring traceability of any content leak independent of device type.
On this page
Watermarking puts your business in control of all aspects of digital assets protection.
Protect from all angles
Works in tandem with other security solutions to protected from other vulnerabilities.
Rapid identification
Time is of the essence when it comes to protecting your revenue.
Streamlined deployment
Numerous pre-integrations with chipset vendors, UHD set-top box makers and smart TV vendors.
Fast, convenient & automated
Blind extraction of payload with pirated content without requiring the original.
Pre-integrated with major SOCs
Implementation is easy and will not divert time or resources.
- Analog Copy
- Cropping
- HDMI Copy
- Aspect Ratio Manipulation
- Digital Copy
- Rotation
- Camcorder / Re-streaming
- Distortion
- Scaling
- Compression
- Geometric Manipulation
Premium content protection to safeguard your revenue.
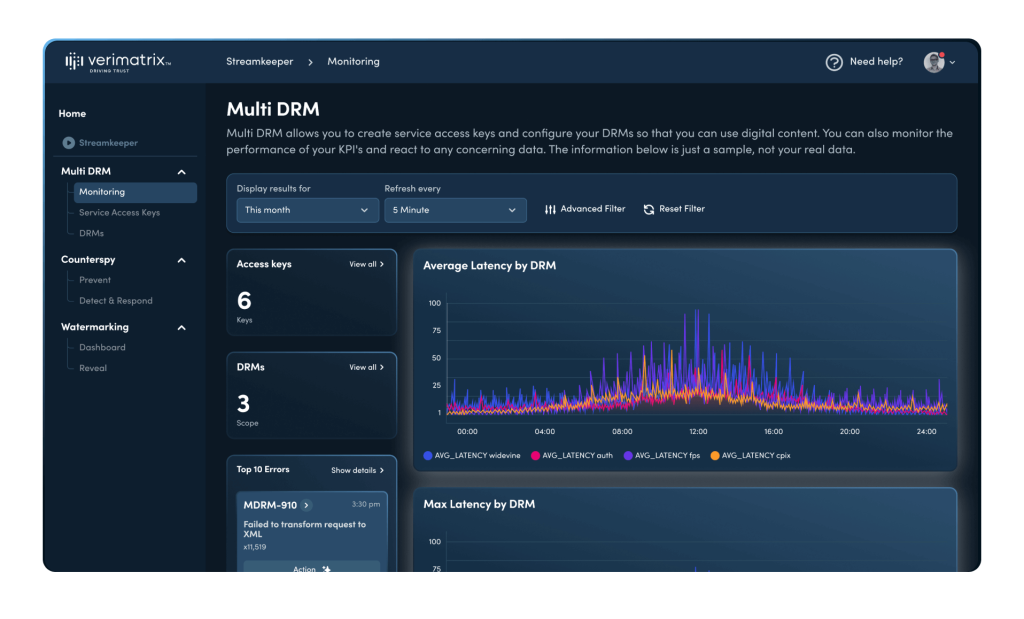
Comply with stringent security requirements and gain access to the premium content viewers want. Verimatrix Watermarking delivers client and server-side protection of live, linear and on-demand video.

Protect or plunder: Taking action against content piracy
A new data- driven approach can target the riskiest behaviour with surgical precision: cutting off criminals while improving the user experience for everyone else.
How Watermarking works
Our watermarking cloud service processes the content pre-encoding and seamlessly integrates with your workflow to identify both the source and target of distribution, ensuring traceability of the content leak.
Using Watermarking in combination with Counterspy enables you to take immediate action once the piracy is identified.
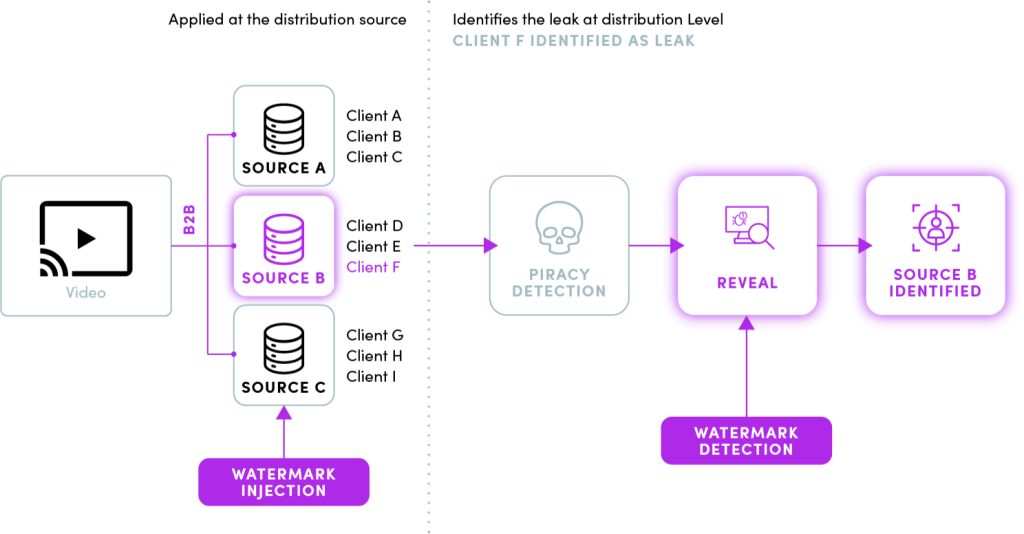
For best-in-class protection, combine Watermarking with Multi-DRM and Counterspy™.
Also see these Streamkeeper products:
Or, upgrade to the full anti-piracy suite:
Streamkeeper Suite
Stop digital piracy with the full anti-piracy suite that includes:
- Multi-DRM
- Counterspy™
- Watermarking
Talk to us
Modernize network security, protect content from piracy, and achieve studio compliance with Verimatrix. Get your free consultation by completing the form.
We’re here to help
- Find the right solution for you
- Point you to relevant resources
- Explain our pricing
Trusted and Recognized
By industry analysts, associations, and peers



Trusted and Recognized
By industry analysts, associations, and peers